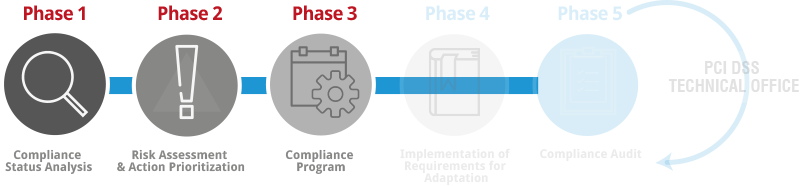
The initial phase to carry out a PCI DSS implementation project begins with a Compliance Analysis in which the aspects of PCI DSS that still need to be implemented to fully comply with the standard are identified. Once the risks linked to the scope of the organization affected by the standard are assessed, an Action Plan will be defined to implement the detected requirements in a prioritized manner.
The objectives of this initial phase of the PCI DSS implementation project are:
- Introduce the project team, the preliminary work schedule, and the project development mechanism.
- Understand how PCI DSS affects the Client. How the organization handles credit card information.
- Obtain the current compliance status of the PCI DSS requirements.
- Limit the compliance environment to the minimum necessary.
- Reduce unnecessary implementation and maintenance costs of the security program.
- Reduce the time required to comply with PCI DSS.
In this stage of the project, all activities related to the assessment of risks to the protection environment defined in the Compliance Environment are carried out, based on the diagnosis performed on the PCI DSS requirements. The objective is to determine in later phases the security measures necessary to mitigate these risks, establish priorities to address them, and achieve compliance with PCI DSS requirements while minimizing effort and investment.
The PCI SSC, through the document PCI DSS Prioritized Approach, defines a methodology for implementing PCI DSS while minimizing the risk of data compromise, based on 6 phases aimed at implementing PCI DSS, highlighting the importance of the standard in fraud protection.
These are the phases described in the PCI DSS Prioritized Approach:
- Stage 1: Remove authentication-related information and limit data retention.
- Stage 2: Protect the environment (perimeter) as well as intranets and wireless networks.
- Stage 3: Secure Applications.
- Stage 4: Monitoring and access control to applications.
- Stage 5: Protect stored cardholder information (card number).
- Stage 6: All other requirements.
The PCI DSS Compliance Program defines the strategy the Client must follow to meet the requirements established by PCI DSS, reduce identified risks, and align security investment with the organization's objectives and needs. This strategy is formalized in a project plan that provides the necessary information to decide which actions to undertake and their justification based on the risk they mitigate.
Selection of Controls and Security Measures
After the risk assessment and action prioritization, the necessary controls or security measures will be defined to implement the actions based on the chosen strategy.
The definition of the controls to be implemented will be carried out taking as reference, in addition to the PCI DSS requirements, the controls established by the ISO/IEC 27001:2013 standard, so that the Client can align PCI DSS requirements with the good practices in Information Security of the standard that enables certification of Information Security Management Systems (ISMS).
Action Plan
After identifying the necessary security controls, Internet Security Auditors will provide the Client with the action plan to implement these controls, including the Self-Assessment Questionnaire (SAQ - Self-Assessment Questionnaire) provided by the PCI SSC when necessary.