Information is one of the main assets of organizations, and its confidentiality, integrity or availability being compromised can endanger their continuity. For this reason, adequate protection systems and proper security management are necessary.
The ISO/IEC 27001 standard was created with the purpose of establishing the foundations of an ISMS (Information Security Management System) using as a reference framework the 12 areas of action defined in the Code of Practice for Information Security Management identified in the ISO/IEC 27002 standard.
- Clear definition and communication throughout the organization of security objectives and guidelines.
- Systematization, objectivity and consistency over time in security actions.
- Analysis and prevention of risks in Information Systems.
- Improvement of information management processes and procedures.
- Staff motivation regarding the value of information.
- Compliance with current legislation.
- Quality image towards clients and suppliers.
Internet Security Auditors proposes an ISO/IEC 27002 Gap Analysis as the first step towards achieving an ISMS according to the international ISO/IEC 27001 standard. This analysis of the current security situation in information systems covers Management aspects (policies, regulations and documented procedures), Legal aspects (laws and contracts) and Technical aspects (architecture, tools and applied technologies).
Understand applicability and the gap
Understand the applicability and the gap regarding ISO/IEC 27002 standards.
Assessment of current security measures
Obtain an independent assessment of the current state of the security measures adopted by the organization.
Raise awareness and responsibility
Opportunity to raise awareness and responsibility across different areas of the company regarding the importance of information security from a management perspective.
Guide the implementation of an ISMS
It is the first step towards implementing an ISMS according to the international ISO/IEC 27001 standard.
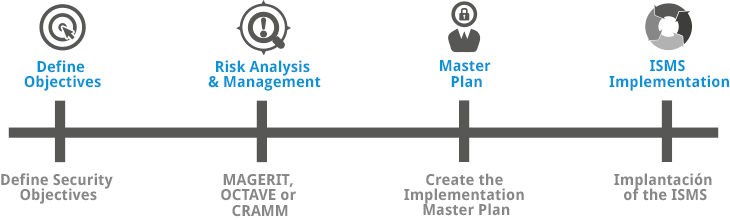
To successfully implement an ISMS, the full involvement and support of management in the project is necessary, as well as a proper ISMS design. This design must identify and document the scope and objectives of the ISMS, develop the company's security policy, inventory the assets included in the scope, and perform a risk analysis to carry out, based on threats, vulnerabilities and impacts, an assessment and subsequent risk management that allows us to select the necessary controls to minimize existing risks and thereby select the applicable controls from the annex of the ISO/IEC 27001 standard.
The objectives of implementing an ISMS can be summarized as follows: