Given the level of globalization and internationalization of companies, institutions, and NGOs, organizations increasingly require transnational travel for their employees, members, or collaborators.
In this scenario, it is essential to conduct an analysis before and during the travel to identify specific risks in the country and territory where the displaced personnel are located, so that the necessary measures can be taken to protect them.
Open-source intelligence (OSINT) has emerged as the most important discipline when it comes to acquiring information. At Internet Security Auditors, we provide the most appropriate cybersecurity solutions for all areas of Information Systems, where Cyber Intelligence is the backbone of a series of Training, Monitoring, and Cyber Investigation solutions.
We use OSINT techniques together with other disciplines such as SOCMINT (Social Media Intelligence) and IMINT (Imagery Intelligence) to monitor any territory and generate actionable intelligence that supports decision-making regarding the protection of displaced personnel.
It should be kept in mind that this is not merely systematic collection, but rather the acquisition and analysis of information to assess whether the content affects the geographical area under analysis, as well as the safety of the type of individuals under study, enabling us to help in decision-making regarding their travel.
The Internet Security Auditors platform monitors, analyzes, and evaluates, with criteria focused on the protection of people, any publication that makes reference to the area of interest defined by the organization.
The organization itself defines the areas of interest (cities and radius of action) as well as information sources, characteristics, and requirements, so that they can be monitored and tracked online using syntactic analysis techniques and artificial intelligence. This content is analyzed using specific algorithms for the analysis of:
Through natural language processing (NLP), a branch of artificial intelligence, it is possible to understand what a person is expressing. This involves morphological, lexical, syntactic, and semantic analysis combined with machine learning, allowing opinions and the associated sentiment level of what is published to be extracted, regardless of the language used.
Using artificial intelligence techniques, images are analyzed and classified by detecting objects, brands, and people. Likewise, terms and/or expressions overlaid or contained in the images are detected and interpreted using OCR techniques, identifying offensive or hostile content through opinion analysis in images, regardless of the language used, which allows moderation of the published content.
Using computer vision and machine learning techniques, we analyze video content to monitor and identify entities that appear in it and may be of interest to the client. On the other hand, we interpret what is being discussed, enabling cataloging and indexing, filtering by highlighted content, or moderating the published content.
Using artificial intelligence techniques, audio is analyzed and classified, detecting offensive or hostile content related to a brand, organization, or individual. For this, opinion analysis techniques are used, regardless of the language used, also allowing moderation of the published content.
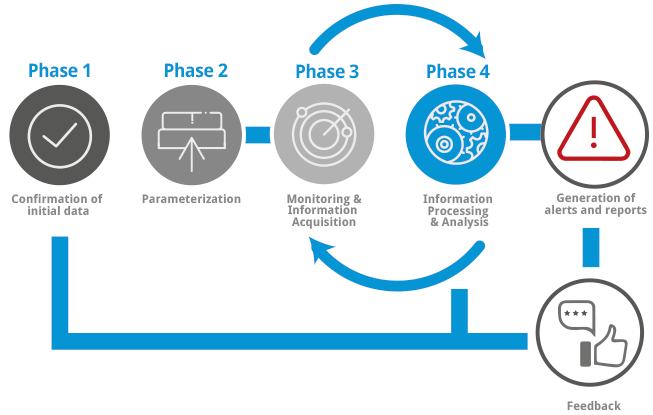
The Digital Brand Monitoring service is carried out in the following phases:
This first phase is optional. If requested, Internet Security Auditors will provide advisory services on the information sources and/or social networks where it may be of interest to deploy probes for monitoring, as well as the most suitable service characteristics given the idiosyncrasies of each organization.
Before starting the monitoring of the specified locations, Internet Security Auditors will request confirmation of the defined scope in order to verify that its characteristics have not changed.
Once the scope characteristics have been confirmed, our digital monitoring platform will be parameterized based on these characteristics, as well as the requirements determined by the client.
The monitoring process will be constant throughout the lifetime of the project. Our platform monitors the selected information sources and detects those publications or interactions that may affect the security of the territory or the displaced personnel.
This is the most complex phase of the process, since the monitoring platform does not simply collect information systematically, but also processes it and provides subsequent interpretation by a cyber intelligence analyst, who identifies the real impact level of the acquired information on the analyzed location.
Based on the information collected, reports are generated that will include the data associated with each of the alerts generated by our Digital Monitoring platform. Each of these reports will include the following information:
- Alert data
- Data of the identified information
- Data of the entity that made the publication
- Data of the analysis carried out