The concept of Cyberspace requires a broader vision of information security concepts than those considered until now. This new concept brings together aspects related to the interaction of people, software, and services on the Internet, supported by ICT environments distributed around the world with a complexity and uniqueness that was unimaginable a few years ago.
To address the challenges of Cybersecurity, which consists of security in Cyberspace, the ISO/IEC 27032 standard emerges, defining guidelines in this field and focusing on two areas: on one hand, covering the gaps not addressed by previous security standards within this broader conceptual scope, where new attacks and associated risks appear; and on the other hand, the collaboration process among the actors operating in the current environment, commonly referred to as a CyberSecurity Framework or CSF.
Considering the challenge of current Cybersecurity scenarios and thanks to the extensive experience of the Internet Security Auditors team, we designed a methodology that enables the implementation of a CSF based on the ISO/IEC 27032:2012 standard, which includes four work focuses or domains:
The Cybersecurity Framework to be developed will take a risk management approach in 4 areas:
Prevention is based on the implementation of measures and controls that limit and contain the impacts of potential cybersecurity events.
Where controls aimed at security management and monitoring of security events are implemented in order to detect and protect against such events.
We must be prepared for potential cybersecurity-related incidents, and this will consist of actions to mitigate adverse elements once they have materialized.
Actions to restore systems and services related to cyberspace, and procedures will be defined to reduce the likelihood of these incidents occurring.
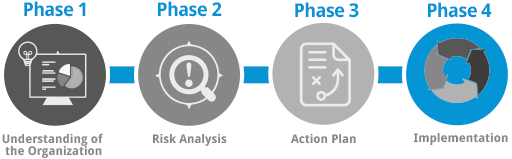
The process followed in our methodology is carried out in five phases.
In this first phase, significant work is carried out to immerse in the company’s processes in order to understand how they operate and how their services make use of Cyberspace. To perform this task, it will be necessary to:
- Review products and services
- Review the security regulatory framework in use
- Gather and review security documentation
- Understand information flows within processes
- Understand the technical security measures implemented, etc.
This phase will also allow the creation of an inventory of assets for the services within scope.
Decision-making regarding the controls and security measures to be implemented must be based on risk management and alignment with the company’s needs. Therefore, in this phase, this assessment will be carried out considering, among others, aspects such as:
- Critical assets
- Threats
- Vulnerabilities
- Impact and risk
- Responsibilities
This task is carried out with alignment to internationally recognized standards, which allow its maintenance and management over time.
In this phase, and thanks to the work carried out in previous phases, the plan will be drafted to determine the prioritization and measures that must be developed to achieve alignment with ISO/IEC 27032:2012 based on business requirements.
This Plan will address different strategies that will include and must be applied at different levels of the organization, including:
- Policies
- Role identification
- Implementation methods
- Affected processes
- Technological controls
This is typically the phase that requires the most effort, as it is where all actions defined in the previous phase are executed according to the Action Plan. It is important to keep in mind that ISO/IEC 27032:2012 aims to require those who implement it to be proactive in security measures, with significant emphasis on prevention mechanisms in processes that make use of Cyberspace.
This project phase will therefore focus on the implementation of controls that must consider the existing maturity level in security management and will take into account, among others, aspects such as:
- Existence of a Security Policy
- Security procedures in SDLC
- Existing frameworks for information exchange
- Staff awareness plans
- Risk Analysis and Risk Management methodology
- ICT monitoring
- Incident management
Additionally, in this phase of the project, additional controls will be established, including:
- Application-level controls: session management, data validation, protection against attacks, authentication processes, etc.
- Server-level controls: secure configurations, patch management, monitoring, periodic reviews, etc.
- Controls for end users: OS updates, application usage, antivirus, security tools and configurations, etc.
- Controls against social engineering attacks: awareness programs, regular testing, security controls, etc.