Law 11/2007 on Electronic Access of Citizens to Public Services recognizes the right of citizens to interact with Public Administrations using electronic means for the exercise of the rights provided for in Article 35 of Law 30/1992, of November 26, on the Legal Regime of Public Administrations and Common Administrative Procedure, as well as to obtain information, make inquiries and claims, submit applications, express consent, file petitions, make payments, carry out transactions, and oppose administrative resolutions and acts.
Article 42.2 establishes the need to create a National Security Framework, which was developed by Royal Decree 3/2010 of January 8 (BOE of January 29). Its main objective is to establish the principles and security requirements for the use of such electronic means, thus enabling the proper protection of information.
We offer a service that not only provides the appropriate consultancy to comply with the National Security Framework, but also the possibility of having a support team in each area of action for the subsequent internal implementation and maintenance process.
The scope of application of the National Security Framework is established in Article 2 of Law 11/2007:
- The General State Administration, the Administrations of the Autonomous Communities, and the entities that make up the Local Administration, as well as public law entities linked to or dependent on them.
- Citizens in their relations with Public Administrations.
- The relations between the different Public Administrations.
Through interviews and other analyses, the degree of adaptation of the Organization to the ENS is assessed, in order to establish the correct guidelines for full compliance.
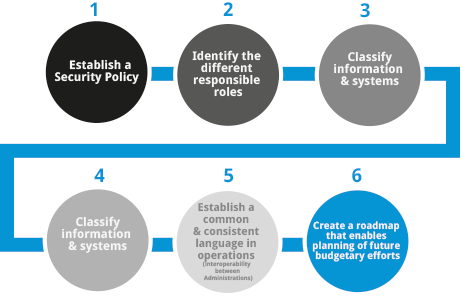
The phases a project goes through are:
Through this phase, minor or major non-conformities are detected, allowing us to identify the differences between the Organization’s current security model and the one proposed by the ENS.
- This gap analysis is organized into the following tasks:
- Analysis of the environment and existing documentation.
- Determination of the asset inventory.
- Designation of representatives by business areas/departments.
- Meetings and minimum security requirements.
After understanding the environment and completing the gap analysis, an Impact Analysis process is carried out for each of the services identified within the project scope.
Once we know the level of compliance with the basic principles and requirements demanded by the ENS, we can proceed with selecting the security measures that will allow us to achieve the appropriate level of compliance:
- Organizational Framework.
- Operational Framework.
- Protection Measures.
Upon reaching this phase, the information systems defined in the project would already be ready to be audited to verify proper compliance.